RabbitMQ vs Apache Kafka: Comparing Message Brokers and Event Streaming Platforms
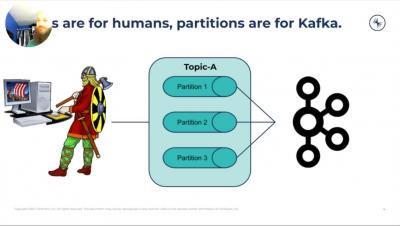
In an event-driven architecture, event routers are the components that connect event consumers to event producers. Not all implementations of event routers are the same, nor do any of them offer an all-purpose solution, so deciding which one to use depends on your use case and project's needs. Understanding their capabilities and limitations provides key insights that empower you to confidently decide which one to use and prepare you to navigate its shortcomings.