Systems | Development | Analytics | API | Testing
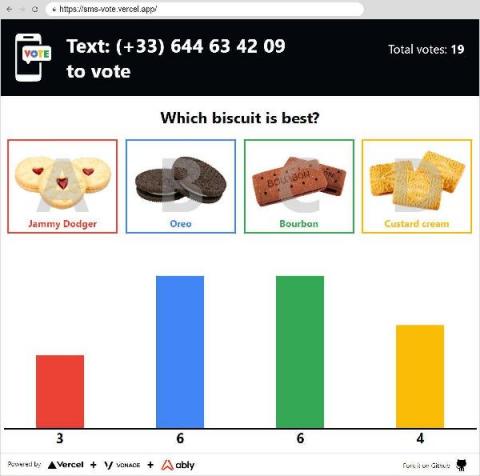
Building a realtime SMS voting app... In the web.
Allow me to set a scene - You’re a speaker at a conference in a large venue. During your talk you’d like to poll your audience to find out whether they use a Mac, Windows or Linux. You’ve got an interactive chart in your slides which will update as the audience votes on your web app. But there’s a hitch, you — as the speaker, have access to a private WiFi, but your attendees don’t have that.
Bitrise for Indie Developers | A walkthrough by Kevin Toms
10 Indispensable Software Deployment Tools
Software Deployment Tools (SDTs) help make software systems available to the target endpoints in a network from a central location. They include installation, distribution, configuration, upgrade, and management tools. All software applications need to be upgraded regularly, require new features from time to time, need security reinforcements against new and coming threats, require updates to remove bugs, and so on.
Rollbar Academy: Rollbar Analytics
A Guide to Data Privacy and Data Protection
6 Mistakes to Avoid When Handling PII
WordPress APIs & DreamFactory
How Your API Ecosystem Can Deliver Benefits to Your Business
The 4 keys to a successful manufacturing IIOT pilot
If you have read our previous post focusing on the challenges of planning, launching and scaling IIOT use cases, you’ve narrowed down the business problems you’re trying to solve, and you have a plan that is both created by the implementation team and supported by executive management. Here’s a plan to make sure you’ve got it all down. Think of these success factors like the legs of a kitchen table and the results that you desire, a bowl of homemade chicken soup.