Systems | Development | Analytics | API | Testing
Bringing Gateway API for Mesh to Kuma
The release of Kuma 2.3 brings experimental support for GAMMA (Gateway API for Mesh Management and Administration) resources. Kuma has long supported Gateway API with the built-in gateway for ingress traffic but with GAMMA support, users can specify how to route and modify in-mesh traffic using the well-known HTTPRoute resource from Gateway API. Gateway API is a project focused on improving the APIs around networking between services in Kubernetes clusters.
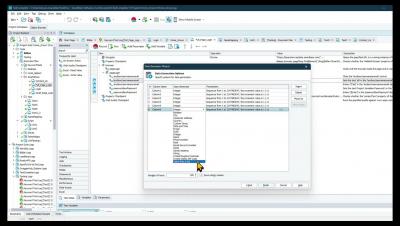
Simulating Backend Systems For Use in UI testing with ReadyAPI
Data Generation in Test Complete
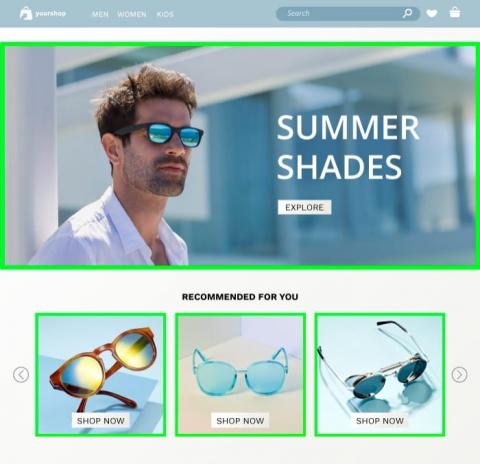
Your Content Changes; Your Layout Doesn't. Make Sure it Always Looks Good.
Visual tests are essential for making sure your website looks good, but they also can be challenging to run if your website has a lot of dynamic elements. In a typical visual regression test, your goal is to compare new website versions against previously set baselines to check that unnecessary changes don’t accidentally get loaded to production.
Version control APIs with Git integration
Available in beta, we have introduced new version control REST APIs for Git integration in the 9.3.0.cl release of ThoughtSpot Analytics Cloud. ThoughtSpot administrators can now link their instances to a GitHub repository and utilize continuous integration and deployment (CI/CD) best practices to effectively manage their organization's analytic content throughout its lifecycle.
Get Gravitas and Go Amazonian: Kong Validated for AWS Graviton3, Amazon Linux 2023 OS
Today, we’re thrilled to announce that Kong Enterprise and Kong Konnect Data Planes are now validated to run on AWS Graviton3 processors and Amazon Linux 2023 OS. As an APN Advanced Tier Partner of AWS, we were delighted to have the opportunity to benchmark Kong Enterprise running on AL2023 and Graviton3.
Kong Mesh 2.3 Improves Security, Flexibility, and Resiliency
Kong is proud to announce the release of the latest version of Kong Mesh 2.3. In this release, Kong Mesh continues to build upon the enterprise-grade service mesh in the critical areas of, security, flexibility, and resiliency. As organizations continue to leverage APIs to deliver digital experiences they rely more heavily on the underlying infrastructure that a mesh provides.
Multi-Factor Authentication Support in AlertSite
In the dynamic realm of synthetic monitoring, where ensuring the performance and availability of critical aspects of web applications is a must, an important aspect has been missing – support for monitoring sign-in processes that use Multi-Factor Authentication (MFA). Until now, no synthetic monitoring product on the market has adequately addressed the challenge of monitoring transactions that require the input of MFA code.