Systems | Development | Analytics | API | Testing
5 Common Mistakes When Developing APIs
A Beginner's Guide to Microservices
The Life of an API Gateway Request (Part 1)
The Life of an API Gateway Request (Part 1)
The inner workings of an API gateway request can be difficult to understand because of its scale. To provide some orientation, we will use the real world as a reference, from planet-spanning infrastructure to a person eating a chocolate bar (processing a server response in a plugin). This series will divide the abstraction space of how Kong Gateway processes requests into four different layers.
Managing APIs at Scale in a Kubernetes Environment - Part II
In the last blog, we discussed the challenges in managing APIs at scale in a Kubernetes environment. We also discussed how deploying a Kubernetes Ingress Controller or an API gateway can help you address those challenges. In this blog, we will briefly touch upon some of the similarities and differences between an API gateway and Kubernetes Ingress. We will also discuss a unique approach offered by Kong for the end-to-end lifecycle API management (APIM) in Kubernetes.
13 Great Reasons To Add APIs To Your Business
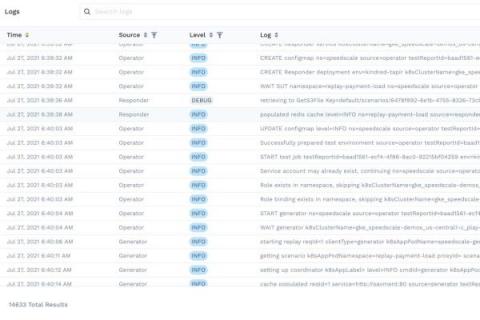
Application Logging in 2021
Have you ever written a Hello, World! application? In most of these tutorials the first step is to log words to the console. It's an easy way to understand what is going on with your application and readily available in every programming language. The console output is incredibly powerful, and it has become easier than ever to capture that output as logs. As your application grows and evolves you need to implement a structured application log approach.
Token-Based Access Control With Kong, OPA and Curity
As APIs and microservices evolve, the architecture used to secure these resources must also mature. Utilizing a token-based architecture to protect APIs is a robust, secure and scalable approach, and it is also much safer than API keys or basic authentication. However, token-based architecture comes in varying maturity levels, as outlined by the API Security Maturity Model.