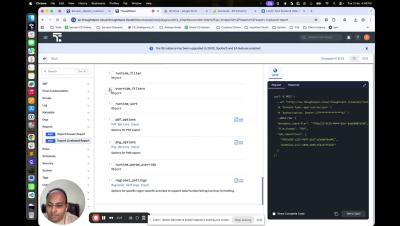
Exporting Liveboard Reports using API with ThoughtSpot
Tired of manual reporting workflows holding back your team? Learn how to scale your data distribution by mastering Liveboard exports through both the UI and ThoughtSpot’s REST API v2. In this walkthrough, we dive into the technical details of capturing specific tabs and formatting reports in high-quality PDF and XLSX. We’ll show you how to use identifiers and filters to customize insights—like a brand manager automating reports specifically for Coca-Cola—so your stakeholders get exactly what they need, when they need it.