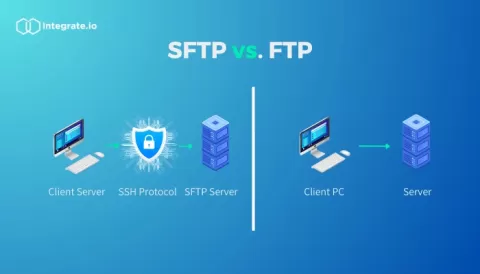
SFTP vs. FTP: Understanding the Difference
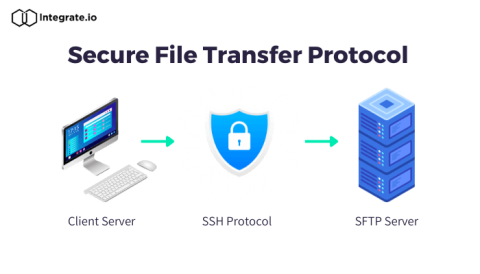
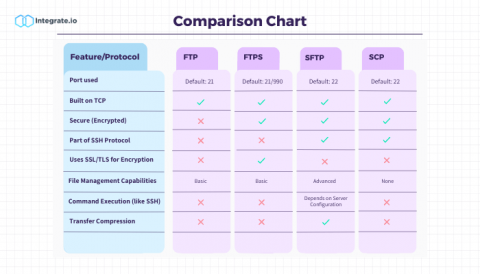
When transferring data, especially in the context of Extract, Transform, and Load (ETL), the choice of protocol matters. Both SFTP and FTP provide solutions, but their intrinsic differences could greatly influence the outcome in terms of security and functionality. Here's everything you need to know about SFTP vs. FTP for ETL.