Systems | Development | Analytics | API | Testing
Snowflake Announces Cyber Essentials Plus Certification
Ensuring a seamless data experience that complies with regulatory frameworks, particularly in the public sector, is crucial. Research from the U.K. government found as many as 32% of businesses and 24% of charities suffered online breaches or cyberattacks in the last 12 months. In this increasingly interconnected world, national stability depends on thoughtful data governance and safeguarding.
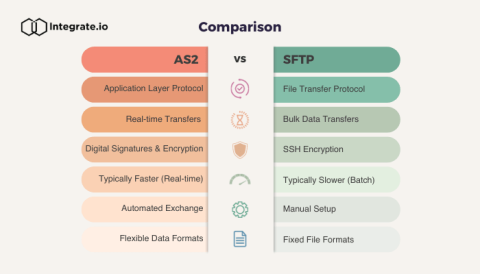
AS2 vs. SFTP: Key Differences & How to Choose
Get started with security: Vite, React, and Ably Token Requests for API access
SaaS APIs typically require some kind of authentication to allow access. While there are many ways that APIs can implement authentication, one popular choice is using secret keys as the scheme. Exposing secret keys directly to a client application however can create security risks, so how can client applications based on libraries like React securely access SaaS services? Many APIs, including Ably, offer an additional client-oriented token authentication system.
How We Implemented Zero Trust in Choreo
In the past, enterprise software focused on protecting network access through on-premises firewalls and VPNs, working on the assumption that everything within the network was secure. However, today, as accessing data has extended beyond on-premises locations to cloud and hybrid networks, SaaS platforms require a security model that can address a broader range of attack vectors. Zero Trust security addresses this pressing need.
Demystifying SFTP Data Transfer: A Step-by-Step Tutorial
Managed Detection & Response Leaders Embrace Data and Analytics to Stay Ahead
The Managed Detection & Response (MDR) industry finds itself in a new era with unprecedented challenges from platform giants and the migration of the attack surface to the cloud, with innovation becoming a requirement for survival. Companies built to provide clients with 24×7 “eyes on glass” now find themselves at the intersection of rapid technological advancements and evolving threat landscapes.