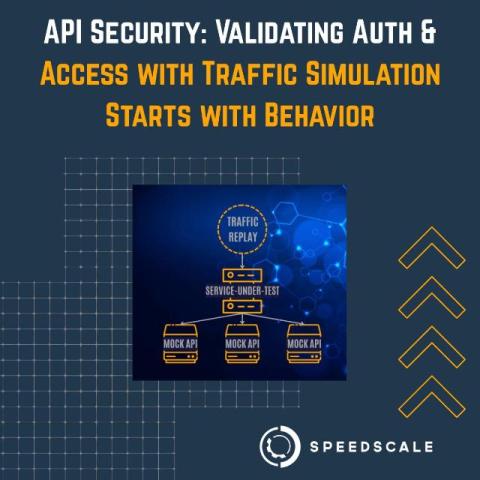
API Security: Validating Auth and Access with Traffic Simulation Starts with Behavior
Security breaches rarely begin with a hidden zero-day exploit or a complex web of escalated hacks. They often start in very simple ways – an internal team member is breached, a permission is misconfigured, an overly permissive API endpoint is overlooked, or a JWT simply doesn’t expire. An API, or application programming interface, is a set of protocols and tools that enable different software systems to communicate and exchange data, making them essential in modern software development.