Systems | Development | Analytics | API | Testing
Dynamic Testing: Your Complete Guide To Runtime Software Testing
Every developer has been there, our code looks perfect on paper, passes all static checks, and seems bulletproof. Then the production cause hits, and suddenly everything falls apart under real user behaviour. The gap between “code that looks right“ and “code that works right“ is where dynamic testing shines. In this blog, we will learn about what dynamic testing is, why dynamic testing is needed in software development and how keploy assist in dynamic testing.
Why API Authentication Is Crucial For Modern Application Security?
Ever been curious about how your app is able to determine if an incoming request is coming from a trusted user or an attacker? In a world where APIs power everything from mobile apps to banks, securing the APIs that underpin them is no longer a nicety but a necessity. One vulnerable endpoint can open the door to data breaches, account takeovers, or even worse. That’s where API authentication comes in.
WSO2's Customer Satisfaction Remains High in H1 2025
At WSO2, our mission is to deliver exceptional digital experiences. We believe that this commitment, combined with our company culture rooted in honesty and transparency, is why organizations worldwide continue to place their trust in us. We're thrilled to share our customer satisfaction scores for the first half of 2025. These results, which reflect our dedication to our customers, include a Net Promoter Score (NPS) of 61 and a Customer Satisfaction (CSAT) score of 4.46 out of 5.
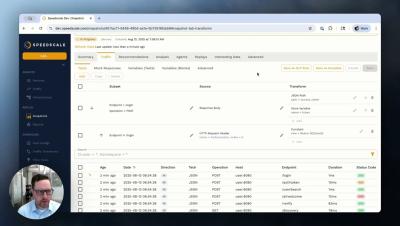
Transforming Snapshots with Templates
Ever wished you could save and reuse your API traffic transformations? With Speedscale's new snapshot templates feature, you can! In this demo, we'll walk you through how to: Find and filter API traffic to create a snapshot. Transform sensitive data, like authentication tokens, with templates. Apply those saved templates to new snapshots instantly, saving you time and ensuring consistency. Whether you're looking to automate your testing or handle sensitive data more efficiently, our new templates feature makes it easier than ever to manage your API snapshots.
Analyzing OpenTelemetry Logs in Moesif for Operational and Business Insights
As your application grows, the volume of telemetry data expands with it. Every additional service, customer, and feature generates more log entries. It becomes harder to quickly isolate the events that actually matter. Without the right tools, finding a single root cause can feel like searching for a needle in an ever-growing haystack. You may have already been using log search tools to find and act on errors. However, those tools rarely connect that data back to your API traffic patterns or metrics.
Moesif + Gloo Gateway: Deep API Analytics and Observability at the Edge
Solo.io Gloo Gateway gives teams a reliable way to secure, route, and monitor API traffic in real time. With its high-performance Envoy core and Kubernetes-native design, it meets the demands of distributed applications and modern service architectures. However, performance metrics alone don’t reveal how developers engage with your APIs or why adoption stalls.
AI-Generated SQL: Enterprise Dream or Security Nightmare?
The idea of using an AI like GPT-5 or any LLM based tool to generate SQL from natural language sounds like a productivity goldmine. Ask the AI a question, and it automatically writes and executes the perfect query. Insight on demand. No SQL expertise needed. But beneath this automation lies a serious threat. Giving AI systems free rein to generate and run SQL against your production database is not just risky—it could be catastrophic.
Webhook Triggers for Event-Driven APIs
Webhooks are a smarter way for APIs to communicate in real-time. Unlike polling, which constantly checks for updates, webhooks automatically send notifications when specific events occur. This makes them faster, more efficient, and resource-friendly. Here’s how they work and why they matter: What are Webhooks?: They are HTTP callbacks triggered by events, delivering data instantly to other systems.
Zero Trust Architecture Needs Zero Guesswork
The Zero Trust model has fundamentally shifted how organizations secure their applications and infrastructure. Instead of assuming anything inside your network is safe, the Zero Trust security model requires continuous verification of every identity, every device, and every access request across the entire trust model, forcing users and devices to prove that they can access what they are trying to access.