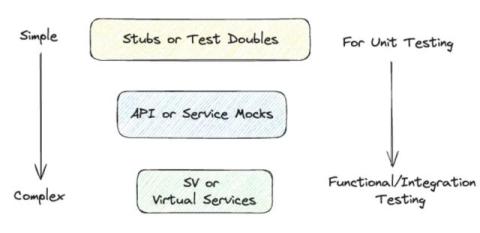
Mock vs Stub: Essential Differences
When discussing the process of testing an API, one of the most common sets of terms you might encounter are “mocks” and “stubs.” These terms are quite ubiquitous, but understanding exactly how they differ from one another - and when each is the correct method for software testing - is critical to building an appropriate test and validation framework. In this blog, we’re going to talk about the differences and similarities between mocks and stubs.