The API-First Alternative to RAG for Structured Data | DreamFactory
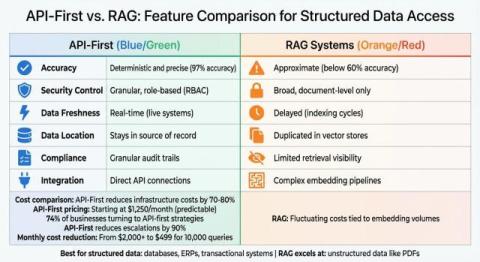
When it comes to integrating AI with structured data, traditional Retrieval-Augmented Generation (RAG) systems often fall short. They rely on indexing and embedding, which can lead to outdated information, security risks, and inefficiencies. Instead, an API-first approach offers a safer, more precise, and real-time solution for accessing structured enterprise data.